How to Encrypt and Securely Transfer Files with GPG
Introduction
In the digital age, the security of sensitive information is paramount. Encryption is a critical tool in protecting data from unauthorized access. Among encryption tools, GnuPG (GPG) stands out for its robustness and versatility. This article delves into the world of GPG, guiding you through the process of encrypting and securely transferring files.
Understanding GnuPG (GPG)
What is GnuPG (GPG)?
GnuPG, or GPG, is a free implementation of the OpenPGP standard. It allows you to encrypt and sign your data and communications. It features a versatile key management system and access modules for various public key directories.
Key Features and Advantages
GPG provides a secure environment for data communication. Its key features include public-key cryptography, a reliable key management system, and compatibility with other encryption standards. The use of GPG ensures that even if data is intercepted, it remains unreadable to unauthorized parties.
Differences from Other Encryption Tools
Unlike proprietary encryption software, GPG is open-source, making it more transparent and trustworthy. It’s also versatile, compatible with multiple platforms and encryption standards.
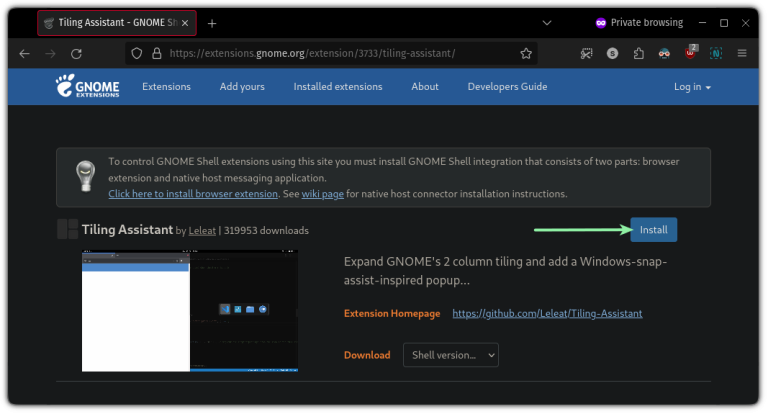
Installing GnuPG
For Windows, macOS, and Linux
Installation methods vary by operating system. For Windows, Gpg4win provides a comprehensive suite. On macOS, GPG Suite is a popular choice, and most Linux distributions come with GPG pre-installed or easily installable via package managers.
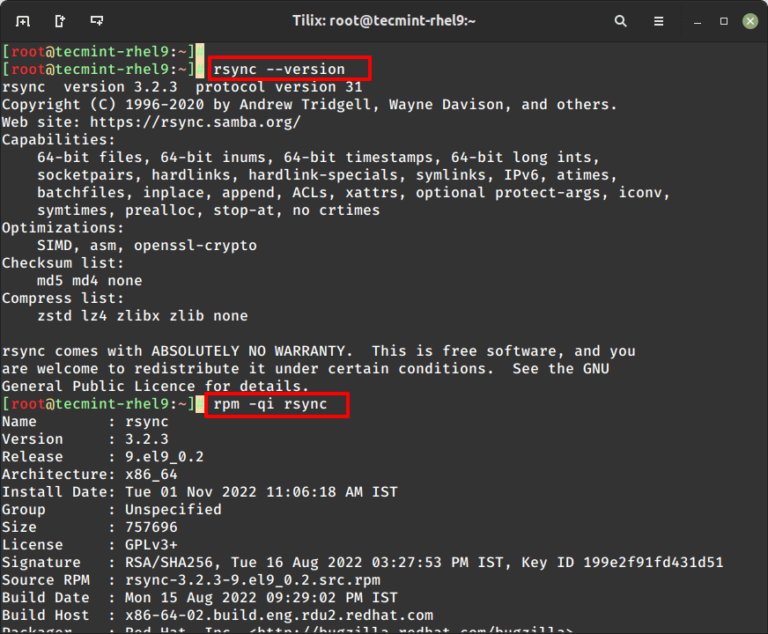
Verifying Installation
Post-installation, it’s crucial to verify the installation. This can be done through command-line interfaces on each OS, ensuring that GPG commands are recognized and executable.
Generating a GPG Key Pair
Generating a key pair is the first step in using GPG. This involves creating a public key, which others use to encrypt data they send to you, and a private key, which you use to decrypt received data.
- Open the command line interface.
- Use the command
gpg --full-gen-keyto initiate key generation. - Follow the prompts to choose the type of key, key size, and validity period.
- Enter your name and email address for the key.
- Protect your key with a strong passphrase.
Understanding Public and Private Keys
The public key can be shared openly, while the private key must be kept secure. The strength of your encryption relies on the security of your private key.
Best Practices for Key Management
- Regularly back up your private key.
- Use a strong, unique passphrase.
- Regularly update your key’s expiration date.
Encrypting Files with GPG
Symmetric vs. Asymmetric Encryption
GPG offers both symmetric (password-based) and asymmetric (key-based) encryption. Symmetric encryption is simpler but less secure, as it requires sharing a password. Asymmetric encryption, using public and private keys, is more secure but involves key management.
Encrypting Files
To encrypt a file for yourself, you can use symmetric encryption:
gpg --symmetric filename
To encrypt for someone else, use their public key:
gpg --encrypt --recipient [email] filename
Decrypting Files with GPG
Decryption Process
To decrypt a file, use the command:
gpg --decrypt filename
Enter your passphrase when prompted. If the file was encrypted with your public key, GPG will use your private key for decryption.
Issues like lost passphrases or keys can be mitigated by maintaining backups and using key revocation certificates in case of key compromise.
Securely Transferring Encrypted Files
When transferring encrypted files, consider the security of the transfer medium. Secure email, encrypted cloud services, or secure file transfer protocols (like SFTP) are recommended.
Large encrypted files may need compression or chunking. Tools like ZIP can be used for compression, while GPG itself can split files into manageable sizes.
Advanced GPG Features
Signing files with GPG ensures authenticity. A revocation certificate is crucial for invalidating your key pair should the private key be compromised.
GPG can be integrated with email clients for encrypted communication. Plugins and extensions are available for popular email clients.
Conclusion
Encrypting and securely transferring files is essential for data security. GPG offers a free, reliable solution for these needs. By following the steps outlined in this guide, users can ensure the confidentiality and integrity of their data.