GPG – Encrypt and Decrypt Files with a Key on Linux
In computing, encryption is a popular and most times the recommended technique of hiding information in a secretive format. GnuPG is one of the useful tools for encrypting information (files) on Linux systems.
GnuPG (also known as GNU Privacy Guard or simply GPG) is GNU’s tool used to encrypt data and create digital signatures that contribute to overall information security. It is a complete and free implementation of the OpenPGP Internet standard that provides an advanced key management solution.
There are two versions of GPG available:
- gpg – a standalone version that is more suited for servers and embedded platforms.
- gpg2 – a version intended for desktops and requires several other modules to be installed.
In some popular Linux distributions such as Debian, the gnupg2 package is a dummy transitional package that provides symlinks from gpg2 to gpg.
This guide shows how to generate a GPG key pair, export and share public keys, encrypt a file, and share and decrypt a file using GPG in Linux systems.
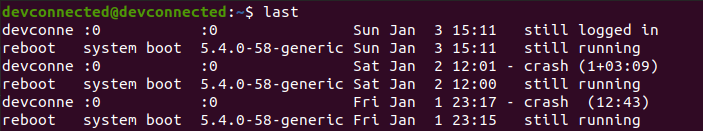
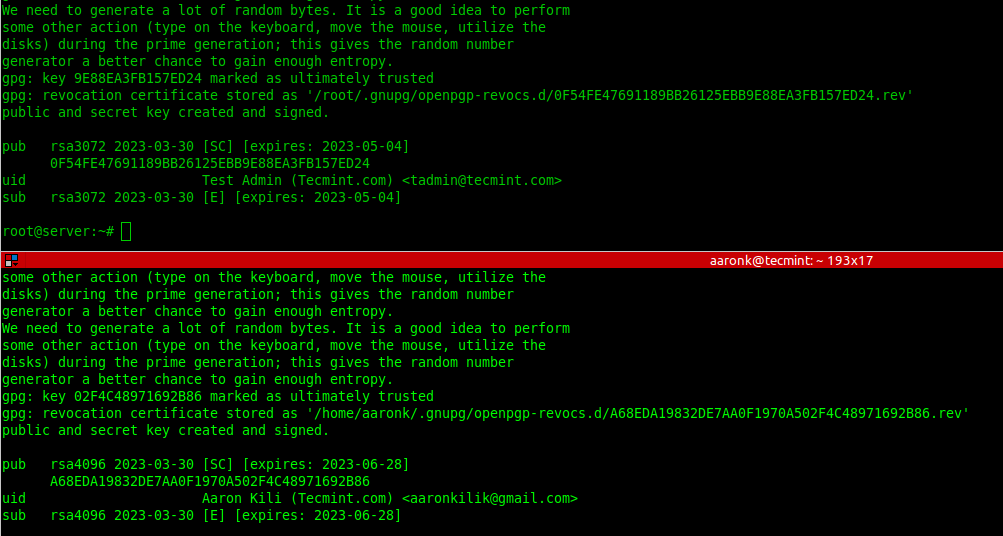
It demonstrates information sharing between two parties:
- Kili Aaron ([email protected]) whose command prompt is [email protected].
- Test Admin ([email protected]) whose command prompt is [email protected].
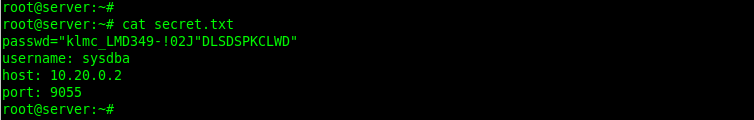
The file shared between the two parties is called secret.txt, which contains a highly sensitive password that the Test Admin wants to share with user Kili Aaron.
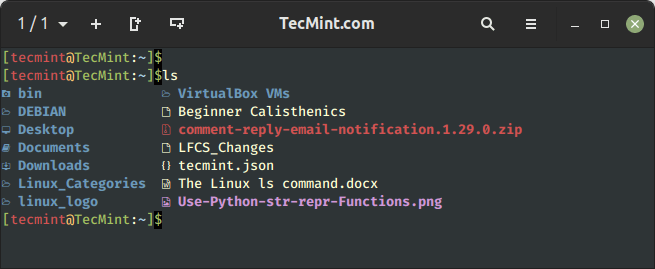
You can view the contents of the secret.txt file that contains the password and other remote access details using the following cat command as shown. It exists on the Test Admin’s server:
# cat secret.txt
Install GnuPG (GNU Privacy Guard) on Linux
To install the GnuPG package, run the appropriate command for your Linux distribution as shown. Note that the gnupg package must be installed on the two systems sharing data.
$ sudo apt install gnupg [On Debian, Ubuntu and Mint] $ sudo yum install gnupg [On RHEL/CentOS/Fedora and Rocky/AlmaLinux] $ sudo emerge -a app-crypt/gnupg [On Gentoo Linux] $ sudo apk add gnupg [On Alpine Linux] $ sudo pacman -S gnupg [On Arch Linux] $ sudo zypper install gnupg [On OpenSUSE]
Generating New GPG Key Pairs in Linux
To generate new key pairs (public and private), run the gpg command with the --full-generate-key flag on both systems and follow the prompts to define the kind of key, the key size, how long the key should be valid, a user ID to identify your key, and a secure passphrase for the key as shown in the screenshot that follows.
$ gpg --full-generate-key
List GPG Key Pairs in Linux
To list the public GPG key you have just created together with other existing keys, run the gpg command with the --list-public-keys flag. To perform a long listing, add the --keyid-format=long flag.
$ gpg --list-public-keys OR $ gpg --list-public-keys --keyid-format=long
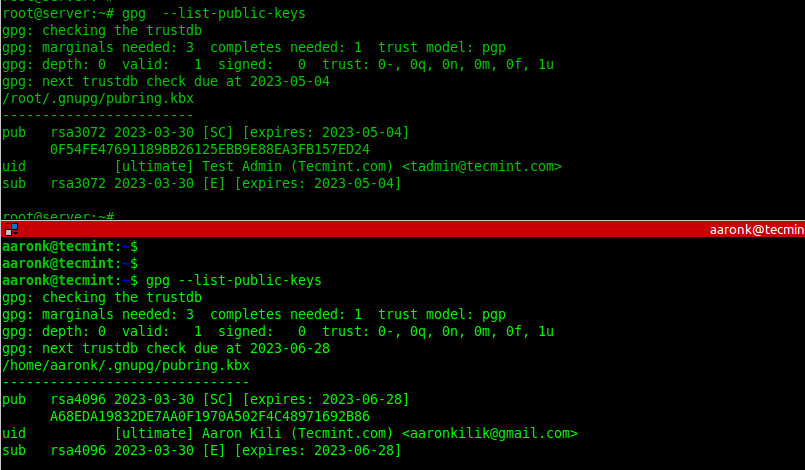
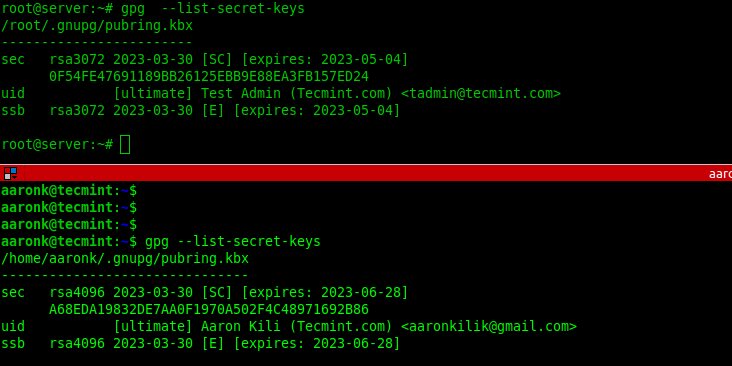
To list the secret GPG key you have just created together with other existing keys, run the gpg command with the --list-secret-keys flag. To perform a long listing, add the --keyid-format=long flag.
$ gpg --list-secret-keys OR $ gpg --list-secret-keys --keyid-format=long
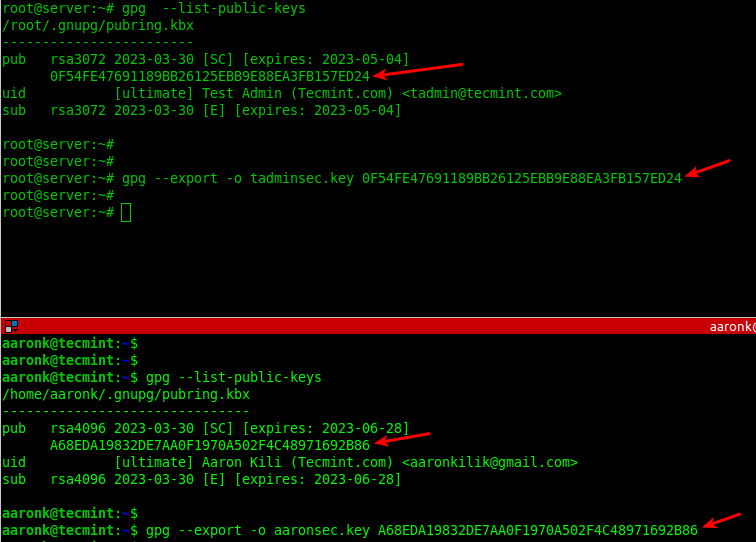
Export Keys with GPG in Linux
Once the GPG key pairs have been generated on both sides, the two parties can export their public keys into a file and share via email or other means.
--------- On Kili Aaron Server --------- $ gpg --list-public-keys $ gpg --export -o aaronsec.key 15B4814FB0F21208FB5076E7A937C15009BAC996 --------- On Test Admin Server --------- # gpg --list-public-keys # gpg --export -o tadminsec.key BC39679E5FF48D4A6AEF6F3437211F0B4D6D8A61
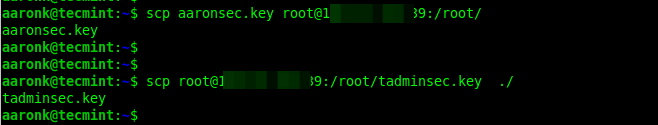
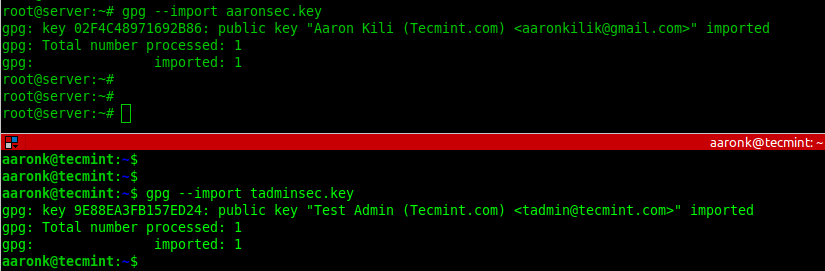
Import Keys with GPG in Linux
Next, exchange the public keys either via email or secure other means such as using the scp command as shown:
$ scp aaronsec.key [email protected]:/root/ $ scp [email protected]:/root/tadminsec.key ./
Next, import the public key from the opposite end into the local system public keyring by adding the --import flag as shown.
# gpg --import aaronsec.key # gpg --import tadminsec.key
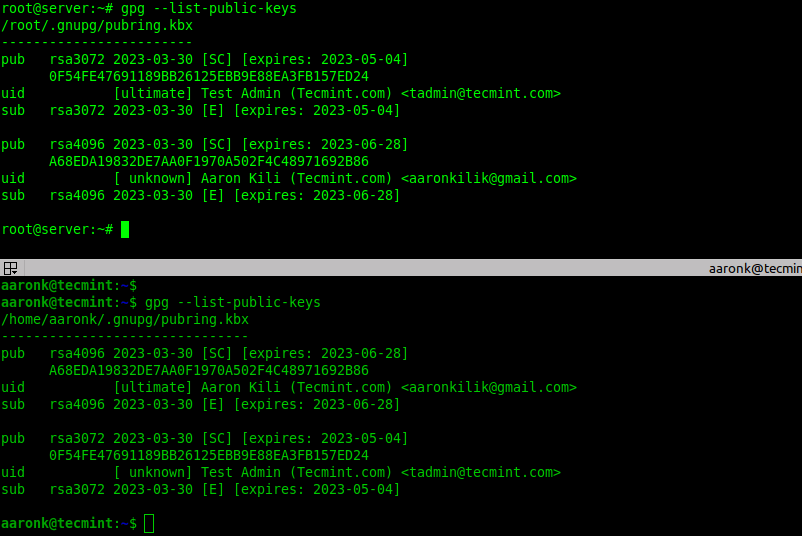
To check if the imported public key exists in the local system keyring, list the available public keys as shown.
# gpg --list-public-keys
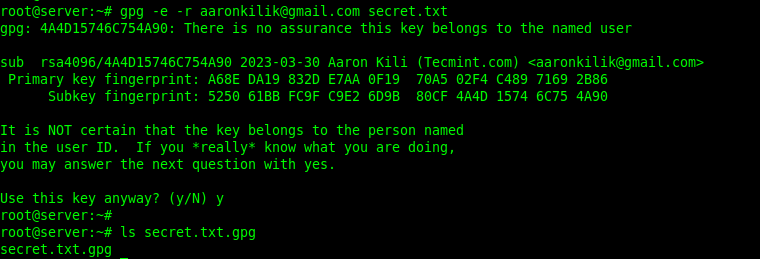
Encrypting Files Using GPG in Linux
Now let’s look at how to encrypt the secret file using gpg keys. For this section, we will run the commands on the Test Admin’s server.
To encrypt a plain text file using the just created GPG key pair, run the following command. The -e or --encrypt flag enables encryption and the -r or --recipient flag is used to specify the recipient ID and secret.txt is the plain text file to be encrypted.
The following command encrypts the file secret.txt using the recipient [email protected]’s public key:
#gpg -e -r [email protected] secret.txt OR # gpg --encrypt --recipient [email protected] secret.txt
If the previous command run successfully, a new file (the original filename ending with .gpg extension) will be generated in the current directory:
$ ls secret.txt.gpg
To store the encrypted information in a different file, use the -o or --output option followed by a filename. In this example, the preferred filename is node_configs:
# gpg -e -r [email protected] -o node_configs secret.txt OR # gpg --encrypt --recipient [email protected] --output node_configs secret.txt
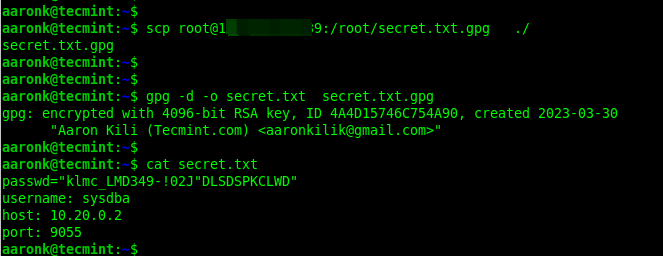
Now share the encrypted file with your partner via email or other secure means.
Decrypting Files Using GPG in Linux
To decrypt a file encrypted using gpg, add the -d or --decrypt flag and specify the encrypted filename. By default, the decrypted information will be displayed in standard output. You can store it in a file using the -o flag as shown.
$ gpg -d -o secrets.txt secrets.txt.gpg $ ls secrets.txt
For more information, see the gpg/gpg2 man page as shown.
$ man gpg OR $ man gpg2
That’s it for the scope of this guide. GPG is a commonly used tool for encrypting and decrypting information or files in Linux. If you have any comments to share about this guide, use the feedback form below.